We have a Steam curator now. You should be following it. https://store.steampowered.com/curator/44994899-RPGHQ/
(Erryone get logged out) Addressing login issue
- rusty_shackleford
- Site Admin
- Posts: 10674
- Joined: Feb 2, '23
- Gender: Watermelon
- Contact:
(Erryone get logged out) Addressing login issue
There will be a one-time change that will cause everyone to be logged out. I apologize for the inconvenience, this is an attempt to fix a persistent issue with certain legacy users having login issues.
Please let me know if anyone has issues staying logged in after this, thank you.
Please let me know if anyone has issues staying logged in after this, thank you.
Last edited by rusty_shackleford on March 4th, 2024, 19:07, edited 1 time in total.
I expected 2FA when re-logging
- rusty_shackleford
- Site Admin
- Posts: 10674
- Joined: Feb 2, '23
- Gender: Watermelon
- Contact:
To be clear, this was a last resort after a long time of troubleshooting. I don't even know if it will fix the issue.
- Ratcatcher
- Turtle

- Posts: 638
- Joined: Feb 2, '23
Well, was it fixed? Having to login again caused me an immeasurable amount of inconveniences and my day is now ruin. I hope it was worth it, at least.
That's what password reset is for lol
I never persist the session (aka I always login) which amounts to one button press when opening this site, because I use a proper password manager.
And you should do too.
And you should do too.
- Analogue Dreams
- Posts: 18
- Joined: Feb 28, '24
So you keep a persistent session of your password manager's database open and unencrypted instead? Why would you avoid keeping cookies that keep you logged in, but use a password manager that stays open and doesn't time out and lets you enter passwords with only one button? Reminds me of using LUKS1 with PBKDF2 and TPM to make it easy for authorities to bypass the encryption entirely, or if they don't have someone who knows how to do that, they could crack such a weakly encrypted password automatically in a few minutes without any technical knowledge anyway.Decline wrote: ↑ March 5th, 2024, 23:59I never persist the session (aka I always login) which amounts to one button press when opening this site, because I use a proper password manager.
And you should do too.
- rusty_shackleford
- Site Admin
- Posts: 10674
- Joined: Feb 2, '23
- Gender: Watermelon
- Contact:
Analogue Dreams wrote: ↑ March 6th, 2024, 07:14So you keep a persistent session of your password manager's database open and unencrypted instead? Why would you avoid keeping cookies that keep you logged in, but use a password manager that stays open and doesn't time out and lets you enter passwords with only one button? Reminds me of using LUKS1 with PBKDF2 and TPM to make it easy for authorities to bypass the encryption entirely, or if they don't have someone who knows how to do that, they could crack such a weakly encrypted password automatically in a few minutes without any technical knowledge anyway.Decline wrote: ↑ March 5th, 2024, 23:59I never persist the session (aka I always login) which amounts to one button press when opening this site, because I use a proper password manager.
And you should do too.
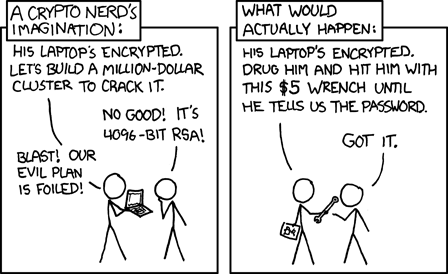
No.Analogue Dreams wrote: ↑ March 6th, 2024, 07:14So you keep a persistent session of your password manager's database open and unencrypted instead?
Because it is convenient.Why would you avoid keeping cookies that keep you logged in, but use a password manager that stays open and doesn't time out and lets you enter passwords with only one button?
Wrong/Invalid comparison.Reminds me of using LUKS1
Password managers exist for using different passwords across multiple sites, so the leak of one website's DB does not cause your account to be taken over on another website. The local state of the encryption (if there's even one) is completely secondary to the password managers main purpose.
Please be dumb somewhere else.
Last edited by Decline on March 7th, 2024, 00:40, edited 2 times in total.
Full disk encryption protects against accidental discard of sensitive information, which is a common occurrence in organizations.rusty_shackleford wrote: ↑ March 6th, 2024, 08:21Analogue Dreams wrote: ↑ March 6th, 2024, 07:14So you keep a persistent session of your password manager's database open and unencrypted instead? Why would you avoid keeping cookies that keep you logged in, but use a password manager that stays open and doesn't time out and lets you enter passwords with only one button? Reminds me of using LUKS1 with PBKDF2 and TPM to make it easy for authorities to bypass the encryption entirely, or if they don't have someone who knows how to do that, they could crack such a weakly encrypted password automatically in a few minutes without any technical knowledge anyway.Decline wrote: ↑ March 5th, 2024, 23:59I never persist the session (aka I always login) which amounts to one button press when opening this site, because I use a proper password manager.
And you should do too.
- Ranselknulf
- Turtle

- Posts: 783
- Joined: Feb 3, '23
Jokes on them. My laptop is encrypted with a biometric dick print reader.rusty_shackleford wrote: ↑ March 6th, 2024, 08:21Analogue Dreams wrote: ↑ March 6th, 2024, 07:14So you keep a persistent session of your password manager's database open and unencrypted instead? Why would you avoid keeping cookies that keep you logged in, but use a password manager that stays open and doesn't time out and lets you enter passwords with only one button? Reminds me of using LUKS1 with PBKDF2 and TPM to make it easy for authorities to bypass the encryption entirely, or if they don't have someone who knows how to do that, they could crack such a weakly encrypted password automatically in a few minutes without any technical knowledge anyway.Decline wrote: ↑ March 5th, 2024, 23:59I never persist the session (aka I always login) which amounts to one button press when opening this site, because I use a proper password manager.
And you should do too.
If they want to forcibly take my password, then they'll have to grab my penis.